Other DMS Configuration
See the Digital Messaging Server Options Reference for information on the configuration options available.
Options for a particular monitor override the general channel options.
You must set the following Java VM properties according to which DMS channels are used in your environment:
| Channel(s) | Options |
|---|---|
| Chat mode only is used in all DMS channels |
|
| Paging mode only is used in all DMS channels |
|
| Both chat and paging modes are used in DMS channels |
|
| DMS channels do not post messages to DMS (for example, a channel for bots) |
|
Enabling proxy server support for DMS (Optional)
Important
Starting with the release of Genesys Driver for use with Apple Business Chat 9.0.002.05, basic authentication over HTTP is supported between the driver and proxy server.- Edit the appropriate file by adding these Java runtime startup options:
- If using Genesys Cloud API Driver for Facebook 8.5.300.09 or earlier, or Genesys Cloud API Driver for Twitter 8.5.300.07 or earlier:
- -DproxySet=true
- -DproxyHost=<host of proxy server>
- -DproxyPort=<port of proxy server>
- If using Genesys Cloud API Driver for Facebook 8.5.300.10 or later, or Genesys Cloud API Driver for Twitter 8.5.300.08 or later:
- -Dhttp.proxyHost=<host of proxy server>
- -Dhttp.proxyPort=<port of proxy server>
- -Dhttps.proxyHost=<host of proxy server>
- -Dhttps.proxyPort=<port of proxy server>
- If using Genesys Driver for Apple Business Chat or Genesys Driver for Genesys Hub (WhatsApp) via HTTPS proxy server:
- -Dhttps.proxyHost=<host of proxy server>
- -Dhttps.proxyPort=<port of proxy server>
- If using Genesys Driver for Apple Business Chat via HTTP proxy server with basic authentication:
- -Dhttp.proxyHost=<host of proxy server>
- -Dhttp.proxyPort=<port of proxy server>
- -Dhttp.proxyUser=<username>
- -Dhttp.proxyPassword=<password>
- -Djdk.http.auth.tunneling.disabledSchemes= (Note that the value of this JVM property must be empty)
- If using Genesys Cloud API Driver for Facebook 8.5.300.09 or earlier, or Genesys Cloud API Driver for Twitter 8.5.300.07 or earlier:
- To enable authentication for the proxy server, add these options as well:
- If using Genesys Cloud API Driver for Facebook 8.5.300.09 or earlier, or Genesys Cloud API Driver for Twitter 8.5.300.07 or earlier:
- -DproxyUser=<username>
- -DproxyPassword=<password>
- If using Genesys Cloud API Driver for Facebook 8.5.300.10 or later, or Genesys Cloud API Driver for Twitter 8.5.300.08 or later:
- -Dhttp.proxyUser=<username>
- -Dhttp.proxyPassword=<password>
- If using Genesys Cloud API Driver for Facebook 8.5.300.09 or earlier, or Genesys Cloud API Driver for Twitter 8.5.300.07 or earlier:
- File to edit:
- Windows: In JavaServerStarter.ini, the [JavaArgs] section.
- Unix and related systems: In dmserver.sh, the last string, namely "$JAVA_EXECUTABLE_PATH/java" -classpath $CLASSPATH $JVMPARAMS $MAINCLASS $*
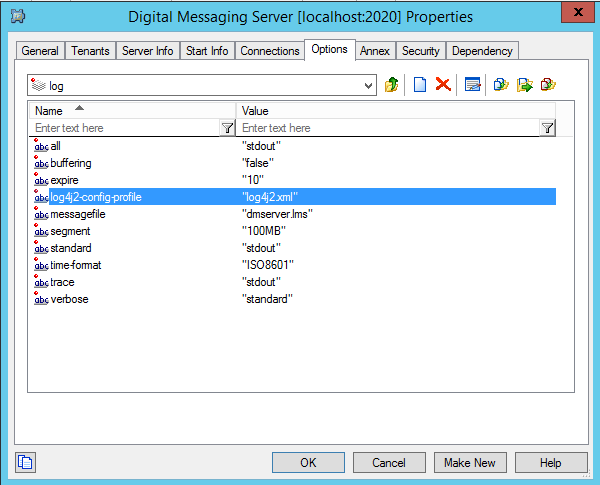
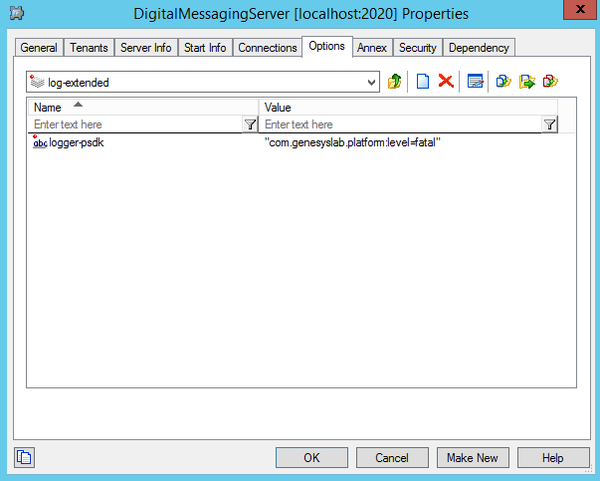
Setting up logging
After an upgrade, ensure that the log4j2.xml file is present in the DMS directory and set up the following logging options:
This page was last edited on November 24, 2020, at 11:25.
Comments or questions about this documentation? Contact us for support!