role
Section: callconcentrator
Default Value: all
Valid Values: A comma-separated list of valid roles
Changes Take Effect: After restart
Specifies the type of data that this ICON instance processes and stores in IDB. The option value must be lowercase. If you use uppercase letters in the option setting, the role defaults to all.
Valid Values:
- all - Stores all types of data.
- cfg - Stores the initial configuration state and a history of configuration changes retrieved from Configuration Server.
- gcc - Stores interaction-related and party-related information; that is, T-Server and Interaction Server data that pertains to voice and multimedia interactions, and the parties associated with those interactions.
- gls - Stores T-Server and Interaction Server data that pertains to agent states and agent login sessions.
- gud - Stores T-Server and Interaction Server data that pertains to the attached data associated with calls.
- lrm - In an environment with License Reporting Manager, stores license reporting data.
- gos - In an environment with the Outbound Contact solution, stores OCS data that pertains to outbound calls and campaigns.
Prefixing an option value with a tilde (~) excludes that type of data from ICON processing, and includes all other types.
Architecture, Components, and Functionality
This topic describes the basic architecture and components of Interaction Concentrator. It also provides a high-level overview of Interaction Concentrator functionality. It contains the following sections:
Basic Architecture
Interaction Concentrator is a Genesys product that collects and stores detailed data from various sources in a contact center that utilizes Genesys software. Downstream reporting systems can access Interaction Concentrator data in near real time.
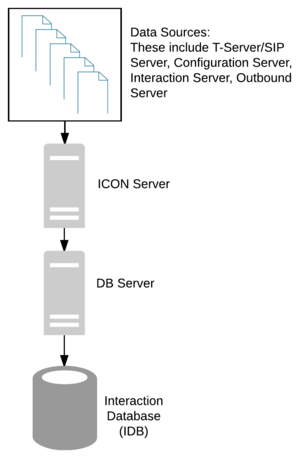
Operating on top of Genesys Framework, the Interaction Concentrator product consists of a server application called Interaction Concentrator (ICON) and a database called Interaction Database (IDB). The server receives data from the data sources such as Configuration Server, T-Server, or particular Genesys solutions; it then stores this data into IDB through Genesys DB Server.
Security Features
Interaction Concentrator supports the following security features:
- Encrypted RDBMSs.
- Hiding TEvent or multimedia-specific attached user data in the ICON log. To specify keys for which the values should be hidden in the ICON log file, configure one—or—both of the following options in the ICON Application object:
- Set the default-filter-type option in the [log-filter] section.
- Explicitly define one or more <key-name> options in the [log-filter-data] section.
- If any attached data is configured to be hidden, ICON debug-level messages might hide all attached data values in the log, not just the values of the keys configured to be hidden. If the default-filter-type option in the [log-filter] section is set to skip, ICON prints an empty string for all KVList pairs in the log file, except those keys that are explicitly configured in the <key-name> options in the [log-filter-data] section.
- If any of the <key-name> options in the [log-filter-data] section are set to skip, ICON might print an empty string, not only for the specified key but also for other KVList pairs in the log file.
Support for Secure Connections
- Starting with release 8.1.1, Interaction Concentrator supports Transport Layer Security (TLS) and TLS-FIPS connections.
- Starting with release 8.1.2, Interaction Concentrator supports client-side port definition, to provide secured connections to T-Server, SIP Server, Configuration Server, and Message Server.
On Windows platforms, support for TLS is integrated into the operating system, and there are no additional requirements to enable Interaction Concentrator to support it. On UNIX-based platforms, you must install the Genesys Security Pack on the Interaction Concentrator host.
In the following scenario, you must configure ICON host security certificate settings at the ICON DAP Application object level:
- You need a secure connection between Configuration Server and ICON configured with the cfg role or the all role.
- The ICON server and the DB Server to which it is connected are on different hosts.
See Securing Connections Using TLS in the Genesys Security Deployment Guide for configuration instructions.
Components and Functions
Interaction Concentrator consists of the following elements:
- ICON server
- Interaction Database (IDB)
The following subsections provide brief descriptions of the Interaction Concentrator components. For more details, see How ICON Works.
ICON Server
The ICON server:
- Performs preprocessing of events received from Configuration Server, T-Server, Interaction Server, and Outbound Contact Server (OCS), according to the role configured for the ICON instance. Roles are configured using the role configuration option. For more information, see ICON Roles.
- Prepares the data that will be stored in IDB. Writes the prepared data from the in-memory queue to the persistent queue and persistent caches. For more information, see Persistent Queue and Persistent Caches.
- Manages the data in the persistent queue and persistent caches.
- Writes data from the persistent queue into IDB.
- Writes data from the persistent cache for configuration data (cfg-sync.db) into IDB.
For detailed information about the configuration options that determine ICON functionality and performance, see the Interaction Concentrator Deployment Guide
Persistent Queue and Persistent Caches
The persistent queue (.pq) is a file that ICON creates and uses to store data before writing it to IDB. The persistent queue also stores information about database-writing requests that are made to IDB. Each ICON instance creates its own persistent queue file (default name icon_dbid.pq), which stores data for all the roles that are configured for that ICON. Data in the persistent queue survives a shutdown and restart of ICON. Alarm thresholds can be used to monitor ICON performance.
For information about the configuration options that control persistent queue functionality, see the Interaction Concentrator Deployment Guide.
Persistent Cache for Configuration Data
There is an additional persistent cache (cfg-sync.db) for the ICON instance that performs the cfg role. This cache plays an important role in maintaining IDB synchronization with the Configuration Database. For more information about the role of the persistent cache in maintaining synchronization, see Populating Configuration Data.
Persistent Cache for Agent Login Session Data
For the ICON instances that perform the gls role, there is an additional persistent cache (default name apstorage.db) for agent login session data. ICON uses this cache to prevent stuck login sessions and to prevent duplicate storage of agent login sessions in IDB. For more information, see Populating Agent Login Session Data and Extracting Agent-Specific Data.
ICON Server Interfaces
The ICON server interfaces with:
- Solution Control Server (SCS) through Local Control Agent (LCA), to control when the ICON server starts and stops.
- Configuration Server, to read Interaction Concentrator application configuration options and other configuration objects and options that affect Interaction Concentrator functionality. (This interface is logically separate from ICON’s connection to Configuration Server as a source of data about contact center resources. See Supported Features and Functionality.)
- Message Server, to log messages to the Central Logger.
Interaction Database
The Interaction Database stores data about contact center interactions and resources at a granular level of detail. IDB is a database optimized for storage (in other words, primarily for inserting data). Interaction Concentrator itself does not provide reporting functionality. You can use IDB as a consistent and reliable data source for downstream reporting applications.
For a high-level description of the IDB architecture, see Introducing IDB Schema. For a complete table structure and descriptions of all IDB tables and fields, see the Interaction Concentrator 8.1 Physical Data Model document for your particular RDBMS.
Stored Procedures
Interaction Concentrator uses a number of stored procedures. Most of these are completely internal to Interaction Concentrator functioning. Therefore, detailed information about them is not relevant for end users.
The following stored procedures are exposed for end-user use and require user input or action:
Purge
- gsysPurgeIR, gsysPurgeUDH, gsysPurgeLS, and gsysPurgeOS—The procedures that safely purge voice interactions, user data history, agent login session, and Outbound Contact data, respectively, from IDB.
- ImportantThese separate purge procedures were discontinued in release 8.1.503.03. If you are using Interaction Concentrator 8.1.503.03 or higher, use gsysPurge81 or (in Oracle environments) purgePartitions811.
- gsysPurge81—An alternative procedure that safely purges voice, multimedia, and outbound interactions; attached data; and agent login session data from IDB.
- ImportantInteraction Concentrator release 8.0.000.32 and earlier includes the prior version of the purge procedure, gsysPurge80, which does not purge Outbound Contact data.
- purgePartitions811—If you are running Oracle 11g or higher and need to purge large amounts of data efficiently, you can create a partitioned IDB that can be purged by truncating partitions.
Custom Dispatchers
- gudCustDISP1 and gudCustDISP2—The stored procedures that customize attached data processing.
Merge
- gsysIRMerge and gsysIRMerge2—The merge procedures that finalize data processing of closed single-site and multi-site interactions.
- gsysIRMergeReset—The procedure that resets the merge procedure to recover from a failed state.
Time-Setting
- gsysInitTimeCode—The stored procedure that populates the G_TIMECODE table, to enable time-interval reporting.
For more information about these stored procedures, see Using Special Stored Procedures.
Supported Features and Functionality
Depending on the role configured for the Interaction Concentrator instance, Interaction Concentrator provides the following features and functionality that support reporting about contact center activities:
- Captures and stores information about the current contact center configuration (objects and associations), and preserves information about deleted configuration objects and terminated associations.
- Captures and stores detailed information about active and completed voice interactions, including switch, DN, time, and routing information about calls and parties. Interaction Concentrator uses a globally unique call identifier. For more information, see How ICON Works.
- Captures and stores detailed information about multimedia interactions (e-mail, non-SIP chat, and custom-designed media such as fax and web forms). For more information, see Integrating with Multimedia.
- Captures and stores detailed information about agent states and login sessions, for agents handling voice as well as multimedia (e-mail, non-SIP chat, other third-party media) and SIP chat interactions. For more information, see Agent States and Login Sessions.
- For voice interactions, functionality includes the option to specify which interaction–the first one or the last one–ICON associates with after-call work (ACW), as well as the option to continue or to interrupt the ACW and NotReady agent states while an agent is handling another call. For more information, see After-Call Work and Not-Ready Agent States. See also the information about configuring agent login session metrics in the Interaction Concentrator Deployment Guide.
- Supports custom agent states, for agents handling voice interactions. For more information, see Agent States and Login Sessions.
- For all types of interactions, captures and stores detailed information about virtual queue usage in interaction processing. For more information, see Monitoring Virtual Queues and Routing Points.
- For voice interactions, captures and stores detailed information about Routing Point (RP) usage in call processing.
- Captures and stores detailed information about interactions that are generated in a network-based contact solution environment.
- Captures and stores detailed information about interactions that are generated in a network call parking environment.
- Stores attached data and captures the history of attached data changes for voice interactions as well as eServices (e-mail and chat) and 3rd Party Media interactions. For more information, see Processing Attached Data.
- Supports customized attached data processing for voice calls. For more information, see Customized Attached Data Processing.
- Captures and stores detailed information about outbound campaigns, including:
- History of campaign processing
- History of chain processing
- Precalculated metrics provided by OCS
- For more information, see Integrating with Outbound Contact.
- Provides a configurable filtering mechanism for certain types of data, to enable the optimization of database size and performance. For more information, see Filtering IDB Data.
- Provides the ability to resynchronize the configuration data in IDB with Configuration Database on demand. For more information, see Resynchronizing Configuration Changes.
- Supports high availability (HA) of all types of data through the use of parallel ICON instances, each with its own instance of IDB, in combination with supplementary data that provides information about the availability and reliability of the data stored in IDB. For more information, see The Interaction Concentrator HA Model.
- Supports near–real-time intraday reporting by writing data to IDB as soon as the data is available (as opposed to after the interaction is completed).
- Provides a sophisticated recognition mechanism, utilizing Inter-Site Call Linkage (IS-Links), to process multi-site interactions. ICON receives information from T-Server regarding the relationship between a given interaction and an interaction at a different site. As a result, complete data is available for reporting across sites. Interaction Concentrator provides a stored procedure to merge the interaction records for multi-site interactions.
- For more information about the merge procedure, see Using Special Stored Procedures.
- Supports multibyte character encoding.
- Stores time information in two formats:
- Greenwich Mean Time (GMT)—As a datetime data type.
- Coordinated Universal Time (UTC) seconds—As an integer data type.
- ICON obtains the time information from the timestamps of the data provider events (for example, T-Server TEvents), in the form of UTC seconds.
- Provides mechanisms to purge voice and multimedia interactions, agent login session data, attached data, and OCS data that is stored in IDB. For more information about the purge procedures, see Purge Procedures.
- If configured with the lrm role, supports Genesys License Reporting Manager (LRM) by storing LRM-specific data. For detailed information see Configuring for LRM Data.