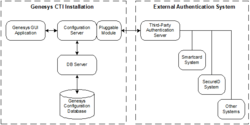
Architecture
The figure below shows connections and information flows when a Genesys CTI installation is integrated with an external authentication system. When logging in to a Genesys application, a user types the user name and password in the standard Genesys Login dialog box. Using the pluggable module, Configuration Server passes the user name and password to the third-party authentication server. The third-party server checks this user’s identity with whatever security system is set up and sends the results to Configuration Server.
If the user is authenticated, Configuration Server continues processing the user login:
- If the user has permission for this application in the Configuration Database, he or she can work with the application and access data in the Configuration Database in a way appropriate to this application type.
- If the user does not have permission for this application in the Configuration Database, Configuration Server generates a login error.
If the third-party authentication server does not authenticate the user, Configuration Server generates a login error. The error message appears on the graphical user interface (GUI) from which the user is trying to log in. The exact wording of the message depends on the specific external authentication system in use.
To provide all diagnostics from the external system to the user, Configuration Server passes error and warning messages from external authentication systems to the client.